Member-only story
Embracing AWS IAM Roles Anywhere

If not a medium member, try using the link here to view it for free.
Please follow and like(clap) the post, if it has helped you.
AWS IAM roles anywhere is an AWS IAM bounded service that was launched quite recently in July 2022.
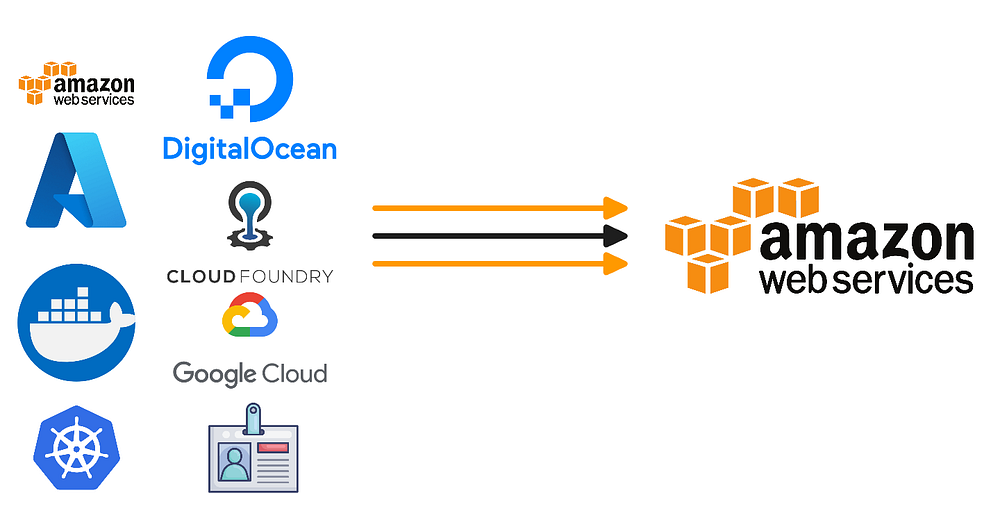
AWS IAM roles anywhere is a service that extends the security benefits of AWS IAM roles to workload resources outside of AWS or services that are non native to AWS.
AWS IAM Roles Anywhere can be leveraged with various types of workloads like:-
➫ on premise apps and functions.
➫ IOT device based apps
➫ external SAAS platforms.
➫ complex PAAS based applications.
➫ cross cloud hybrid applications based on other cloud providers like GCP, AZURE, etc.
➫ not just applications but this can be leveraged for Human beings also, like employees based on their enterprise certificates.
Prior to AWS roles anywhere, any workload that would want to consume an AWS resource would onboard itself on the AWS IAM portal as a user and then get credentials in the form of AWS accessKeyId & secretAccessKey
AWS accessKeyId & secretAccessKey were persistent in nature. If they were compromised one would have to revoke them, generate a new set of accessKeyId & secretAccessKey and then apply them at all the places where they were being used. QUITE a CYCLE and hard to monitor at times for complex applications.
What about STS?

STS is powerful enough to generate a new set of accessKeyId & secretAccessKey on behalf of a federation, etc. But again the client that interacts with STS service still require persistent form of accessKeyId & secretAccessKey to interact with STS service endpoints.
At the end of any service we would always need a pair of accessKeyId & secretAccessKey and…
